On 26 June 2015, the US-Brazil defense cooperation agreement entered into force. This agreement, the first formal defense treaty between Brazil and the US in over thirty years, is ambitious in scope, promoting cooperation in “defense-related matters, especially in the fields of research and development, logistics support, technology security, and acquisition of defense products and services,” as well as “exchanges of information,” “combined military training and education,” “joint military exercises,” “meetings between equivalent defense institutions,” and “exchanges of instructors and training personnel.”Footnote 1 Since the end of the Cold War, the US has signed similar bilateral defense cooperation agreements, or DCAs, with dozens of partners. And the US is not the only country active in DCAs. In 2015 alone, nearly a hundred DCAs were signed between countries as diverse as Indonesia and Turkey, South Africa and Liberia, and Argentina and Russia.
DCAs are a novel form of defense cooperation. At their core, these agreements establish long-term institutional frameworks for routine bilateral defense relations, including coordination of defense policies, joint military exercises, working groups and committees, training and educational exchanges, defense-related research and development, and procurement. As frameworks, DCAs reserve specific details of implementation for protocols and implementing legislation. This flexibility means DCAs can both improve traditional defense capabilities and address such protean nontraditional threats as terrorism, trafficking, piracy, and cyber security. Importantly, DCAs contain no mutual defense or nonaggression obligations. They are not alliances. And unlike the forms of defense cooperation that dominated great-power politics during the Cold War, they are typically highly symmetric, mutually committing signatories to a common set of guidelines.
The growing importance of DCAs is reflected by the controversy they sometimes generate. In 1998 the prime minister of Slovenia faced impeachment proceedings over a DCA with Israel.Footnote 2 An agreement between Belarus and Iran in 2007 provoked public condemnations from both the United States and European Union.Footnote 3 A 1996 DCA between Greece and Armenia led a spokesman for the Turkish government to accuse Greece of “threatening peace and stability in the region” and attempting to “surround Turkey.”Footnote 4 And a 1995 agreement between Australia and Indonesia proved so controversial that it was terminated just four years later.Footnote 5
As Figure 1 shows, DCAs have been proliferating for decades, with a pronounced spike in the years following the Cold War. While the academic study of defense cooperation tends to focus on formal alliances, new alliances are in fact quite rare. As of 2010, nearly as many individual pairs of countries, or dyads, were bound by DCAs as by alliances. Increasingly, when governments institutionalize their defense relations, they turn to DCAs, not alliances. Yet despite their ubiquity, DCAs have been largely ignored by scholars. To the best of my knowledge, there is no political science literature on the topic. This article therefore raises, and attempts to answer, a straightforward question: Why have DCAs proliferated so dramatically? I focus here on DCAs as a dependent variable. Related work examines the effects of DCAs on military and other outcomes.Footnote 6

Figure 1. Growth of bilateral defense cooperation agreements, 1980–2010
In developing a comprehensive theory of DCA formation, I synthesize cooperation theory with network-analytic insights.Footnote 7 States cooperate in order to obtain joint gains.Footnote 8 Exogenous macro-level shifts in the global security environment—including the collapse of the Soviet Union, the decline in interstate war, and the growth of nontraditional security threats—have increased the joint gains of defense cooperation and thus increased demand for DCAs. These systemwide trends translate into specific dyadic influences. Faced with an increasingly complex security environment, states use DCAs to (1) modernize their militaries and improve their defense capacities, (2) improve coordinated responses to common security threats, and (3) align themselves with communities of like-minded collaborators. At the dyadic level, demand for DCAs depends on whether potential partners can help one another meet these goals.
However, joint gains tell only part of the story. Even when demand for cooperation is high, information asymmetries may limit the supply of cooperative institutions. States often lack credible information about one another's trustworthiness, or willingness to cooperate rather than exploit the cooperation of others for unilateral benefit.Footnote 9 Because DCAs involve sensitive national security issues, including access to classified information, coordination of defense policies, and proliferation of sophisticated weapons technologies, they inherently involve issues of trust. States further may lack information about one another's institutional design preferences, such as the preferred scope and precision of formal agreements, which leads to distributional conflicts.Footnote 10 If states are unsure of others’ trustworthiness or unsure about the types of agreements others are willing to sign, the supply of DCAs will remain low.
The logic of joint gains thus does not explain how, despite persistent mistrust and distributional conflicts, states have managed to sharply increase their participation in DCAs. I argue that when governments create DCAs, they reveal information about their trustworthiness and their preferred institutional designs to third-party observers. This information subsequently ameliorates cooperation problems for others, creating favorable conditions for new DCAs. In short, DCAs involve network influence—relations between one pair of states affect relations between others. I consider two specific types of network influence: preferential attachment, where highly active states or “hubs” in the network endogenously attract new partners, and triadic closure, where states that share DCA ties with the same third parties or “friends of friends” are more likely to cooperate directly. These network influences are empirically observable reflections of the underlying informational value of the ties of others.Footnote 11
While network influences have been documented previously in international relations,Footnote 12 I extend those insights by focusing more directly on causal mechanisms. Placebo-like tests, combined with extensive assessment of testable implications, show that the influence of triadic closure and preferential attachment varies according to the quality of governments’ informational environment, which strongly suggests that network influences indeed depend on an informational mechanism. More generally, the empirical analysis indicates that, post-Cold War, network influences quickly became the driving force behind DCA proliferation. Out-of-sample predictions show that although exogenous dyadic factors and corresponding shifts in the global security environment are important determinants of defense cooperation, network influences dramatically improve our ability to predict who signs DCAs, and when. Exogenous influences may stimulate demand, but network influences ensure supply.
What Are Defense Cooperation Agreements?
The universe of defense agreements is large. Treaty records reveal agreements on everything from war cemeteries to nuclear materials to military cartography. The vast majority of these agreements focus narrowly on specific threats or issues, and many follow from unique historical events, such as wars, occupations, state failures, or colonialism. Glaring asymmetries are common, and few agreements are long term. DCAs are different. I define DCAs simply as formal bilateral agreements that establish institutional frameworks for routine defense cooperation. DCAs typically involve relatively symmetric, long-term commitments for both sides, with an emphasis on coordinating core areas of defense policy and encouraging interpersonal contacts. A 2006 DCA between France and India illustrates:
1.1 The purpose of the Agreement is to promote cooperation between the Parties in the defence and military fields, defence industry, production, research and development, and procurement of defence materiel.
1.2 This Agreement shall establish a framework which aims to cover all cooperation activities conducted by the Parties in the field of defence.
1.3 The forms of such cooperation may be specifically defined by way of agreements between the relevant minstries of the Parties.Footnote 13
Beyond this basic definition, DCAs exhibit specific characteristics. First, as Article 1.2 suggests, DCAs are framework treaties. A framework is “a legally binding treaty … that establishes broad commitments for its parties and a general system of governance, while leaving more detailed rules and the setting of specific targets either to subsequent agreements between the parties, usually referred to as protocols, or to national legislation.”Footnote 14 For example, although DCAs often touch on arms trade, the agreements themselves establish only general procedures for procurement and acquisition. Execution of contracts requires subsequent instruments. As Article 1.3 indicates, much implementation occurs separately. Accordingly, leaders often describe DCAs as “legal umbrellas” for defense cooperation.Footnote 15
Second, DCAs emphasize day-to-day interactions in core defense areas, which typically include (1) mutual consultation and defense policy coordination; (2) joint exercises, training, and education; (3) coordination in peacekeeping operations; (4) defense-related research and development; (5) defense industrial cooperation; (6) weapons procurement; and (7) security of classified information. The primary goal of DCAs, then, is to encourage substantive cooperation in these core areas. Importantly, DCAs do not include mutual defense commitments. Public officials often emphasize this fact. Indonesia's defense minister, following a controversial 2007 DCA with China, made this clear: “We only want to improve our defense cooperation with China. We have no intention of signing a defense treaty with China.”Footnote 16
Third, DCAs commonly establish bilateral committees, working groups, and other mechanisms to encourage cooperation. The France-India DCA created the High Committee on Defence Cooperation, tasked with “defining, organizing, and coordinating bilateral cooperation activities.”Footnote 17 Many DCAs also require signatories to develop annual defense cooperation plans that detail summits, policy goals, exercises, exchanges, and pending contracts. An illustrative 2011 DCA between Czech Republic and Moldova stipulates that “the Parties shall work out and approve annually bilateral cooperation plans,” which “shall be worked out by 1 December of the current year.”Footnote 18
Fourth, the language and content of the agreements themselves are highly symmetric, using phrases such as “the Parties” and “the Signatories” in lieu of proper nouns. While asymmetries of course exist in implementation (for example, because of relative power), these are separate from the treaties themselves and best addressed with control variables. Fifth, DCAs are long-term agreements, with a modal length of ten years. Many DCAs are indefinite.
A final important characteristic is that defense partners frequently sign multiple DCAs. They may, for example, replace a prior agreement, or they may simply prefer a piecemeal approach, where they address issue-areas in separate agreements rather than in a single general agreement. In practice, over the 1980–2010 period, about half of countries that signed a DCA subsequently signed at least one more. These subsequent DCAs are novel legal instruments, not merely amendments. I later capitalize on this feature of DCAs to improve causal inference.
Together, these characteristics define DCAs as a distinct form of cooperation. The appendix further describes how DCAs differ from defense and nonaggression pacts, as well as status of forces agreements (SOFAs), strategic partnerships, and confidence-building measures (CBMs). It also includes a full-text example of a DCA. Between DCAs, the primary source of heterogeneity is issue scope. Some agreements, like the France-India DCA, cover all possible areas of defense cooperation. Others are narrower, only partly covering the core issue areas I described. For example, countries may sign one DCA on mutual consultation and another on defense industry cooperation. Governments nonetheless recognize these narrower agreements as elements of a larger defense framework; indeed, they often use general DCAs to pull together various piecemeal efforts. When Bangladesh and China signed a DCA in 2002, their respective prime ministers described the need to “institutionalize the existing accords in defence sector and also to rationalize the existing piecemeal agreements to enhance cooperation in training, maintenance and in some areas of production.”Footnote 19 Whether DCAs take the form of one agreement or a package of agreements, they move toward the singular goal of an institutionalized defense framework. I explore DCA heterogeneity in the appendix and show that the empirical results are robust even when restricting the analysis to the most general DCAs.
The Importance of DCAs
Do DCAs matter? Related work explores DCAs as an independent variable.Footnote 20 Here, I briefly presage those findings. Diplomatic correspondence reveals that states increasingly view traditional military alliances as inadequate to the current global security environment. Shortly after the election of Nicolas Sarkozy in 2007, US diplomats reported that the new French government considered its alliances with African governments to be “patently absurd and out of date.”Footnote 21 France sought to “radically convert the present system of defense agreements,” which were mostly traditional postcolonial defense pacts, and focus instead on “combating illicit trafficking and terrorist acts,” while also encouraging “cooperation on defense and security, favoring the rise in strength of African capacities to carry out peacekeeping.”Footnote 22 African leaders supported these shifts. Comoros, for example, argued for a “new military cooperation arrangement with France,” focusing not on traditional mutual defense issues, but on “training and exchange programs.”Footnote 23
Leaders also frequently tout the material benefits of DCAs. For example, the 2011 annual plan between France and Estonia “lays down nearly twenty different activities,” varying from “training of Estonian air force ground intercept controllers” to “participation of French ships in the Baltops and Open Spirit exercises” to “admitting a French student to the Baltic Defense College.”Footnote 24 Russia's defense minister boasted that the 2016 annual plan with Belarus “stipulates over 130 events and measures.”Footnote 25 According to Indonesia's national news agency, Indonesia's numerous DCAs have allowed it to obtain Sukhoi fighters and Mi-17 helicopters from Russia, platform dock ships and submarines from South Korea, and C-802 missiles from China.Footnote 26 And a 2008 DCA between Latvia and Norway allowed Latvia to increase its peacekeeping presence in Afghanistan and coordinate with Norwegian command.Footnote 27
These historical anecdotes accord with statistical patterns. Figure 2 illustrates the relationship between DCAs and a host of defense and security outcomes. The figure shows that after signing a DCA, dyads are more likely to jointly contribute to peacekeeping missions; more likely to collaborate in joint military exercises; more likely to collaborate on the same side of a militarized interstate dispute (MID); less likely to fight directly in an MID; more likely to engage in arms trade; and more likely to have cooperative interactions overall, as defined by the Integrated Crisis Early Warning System (ICEWS). Related work employs a battery of network selection and coevolution models to address potential omitted variables, reverse causation, statistical dependencies, and other threats to inference, and finds that the basic patterns shown in Figure 2 are extremely robust.Footnote 28 In short, DCAs have a powerful impact on defense and security outcomes.

Figure 2. Effect of DCAs on defense and security outcomes
The DCA Data Set
The DCA data set covers all countries in the world for the period 1980–2010. The appendix discusses the data collection process in detail. Figure 3 illustrates the global diffusion of DCAs. In the 1980s, the DCA network remained sparse, with activity limited to the US, its European partners, and a handful of regional players. In the 1990s, the US continued to be a major player, but Russia, Turkey, and South Africa began showing as much interest in DCAs as the US. By the 2000s, all but a handful of countries had signed at least a few DCAs, with regional powers such as Brazil, India, and China sharply increasing their DCA participation.
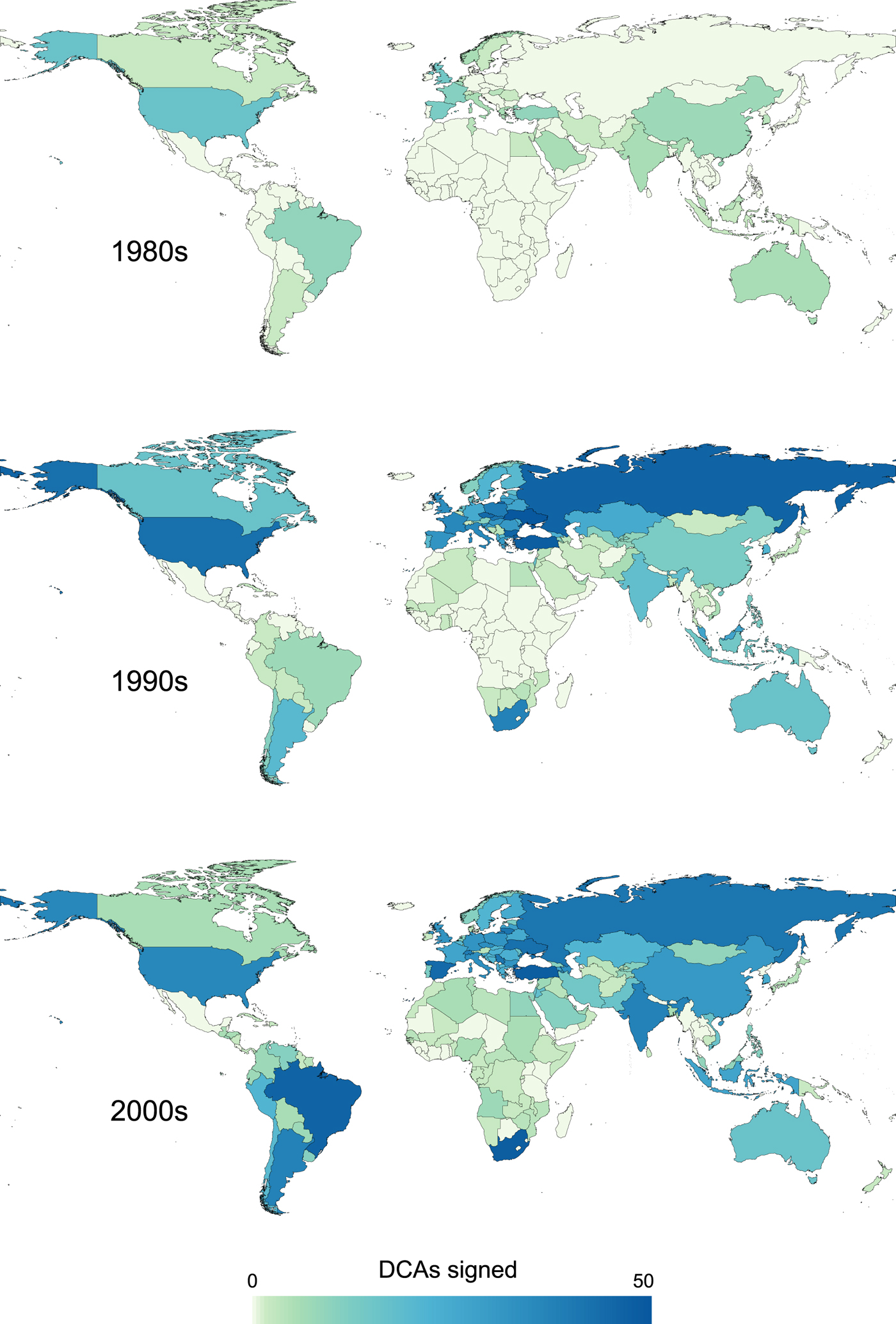
Figure 3. DCA activity across three decades
Global Security, Network Influence, and the Growth of DCAs
The central empirical puzzle with DCAs, illustrated by Figures 1 and 3, is the persistent growth in new agreements. I first theorize DCAs as a type of cooperation problem, distinguishing between demand for DCAs, which is largely motivated by state attributes and exogenous shifts in the global security environment, and supply of DCAs, which is limited by incomplete information. Next I discuss exogenous influences on defense cooperation in greater detail, identifying dyad-level variables that likely affect the probability of DCAs. Finally, I turn to networks. I show that specific network influences reduce informational barriers and encourage DCA proliferation.
DCAs as a Cooperation Problem
Demand for DCAs hinges on the relative payoffs of cooperative versus noncooperative outcomes.Footnote 29 States cooperate to achieve joint gains—gains that cannot be obtained unilaterally.Footnote 30 If those gains are insufficiently large relative to the risks, states have little incentive to cooperate. Exogenous shifts in global security since the 1980s have increased demand for defense cooperation systemwide. At the same time, demand varies across dyads. For some prospective partners, the anticipated gap in payoffs between cooperative and noncooperative outcomes is large, while for others the gap is small. Ceteris paribus, states favor defense partners that are technologically advanced, wealthy, ideologically similar, or otherwise strategically valuable. For example, Hungary pursued defense collaboration with Germany largely because, via the former East Germany, unified Germany possessed large stockpiles of Cold War era spare parts, which were valuable for the Hungarian military.Footnote 31 In short, joint gains affect both the decision to cooperate or not, and the choice of with whom to cooperate.
However, demands for cooperation do not automatically translate into supply. As in other areas of cooperation, asymmetric information poses a fundamental barrier to DCAs.Footnote 32 First, states lack ex ante information about one another's trustworthiness. Systemic anarchy increases the difficulty of credibly conveying trust, which in turn invites fears of cheating and noncompliance.Footnote 33 This asymmetry produces a collaboration problem, where states fail to cooperate because of the potential risk of being “suckered” by exploitative partners.Footnote 34 Collaboration problems can be attenuated if states acquire credible information about one another's trustworthiness, typically conveyed via costly signaling. By deliberately incurring costs that exploitative types would be unwilling to endure, trustworthy types signal their preference for cooperation.Footnote 35 Second, states lack information about one another's preferences over institutional designs, such as the scope, depth, duration, and precision of bilateral agreements.Footnote 36 This asymmetry produces a coordination problem, or a disagreement over how the gains of cooperation should be distributed.Footnote 37 States may refrain from revealing their preferred institutional design out of fear that doing so will lead potential partners to choose a different outcome. Yet, strategically withholding this information also lowers the probability of mutually acceptable bargains.Footnote 38 Substantive cooperation typically involves both coordination and collaboration.Footnote 39
DCAs show strong evidence of collaboration problems. When governments coordinate their defense policies, pool defense-related research-and-development (R&D) resources, transfer sophisticated weapons and military technologies, exchange classified information, hold joint exercises, and so on, they engage in inherently risky activities that create opportunities for exploitation. The key danger in signing a DCA with an untrusted partner is that the partner might ultimately employ the gains of cooperation for its own strategic advantage. In the event of direct confrontation, the improvements in military capacity that DCAs enable—better training, access to classified material, first-hand knowledge of others’ tactics and operating procedures—can be readily used to exploit a nominal defense partner. These concerns further extend to relations with third parties, both governmental and nongovernmental. For example, the US has long worried that military cooperation with countries like Saudi Arabia and Pakistan indirectly supports extremist organizations. More benignly, DCA partnerships also involve managerial concerns about the ability of partners to fulfill their obligations.Footnote 40 In 2007, for example, the Japanese self-defense force unintentionally leaked classified details of the US-built Aegis weapons system, causing a furor in the US defense community.Footnote 41 For all these reasons, DCAs require credible assurances of trustworthiness.
If states lack sufficient ex ante trust (that is, prior to treaty signature), cooperative efforts may fail.Footnote 42 Unsurprisingly, the language of trust permeates DCA negotiations. Australia's controversial 1995 DCA with Indonesia reflected the new reality that Australia “no longer sees Indonesia as an expansionist threat.” Australian Prime Minister Paul Keating bluntly stated: “It is a declaration of trust.” Indonesia's President Suharto echoed the sentiment, asserting that “if there is still suspicion about Indonesia, then it should be eliminated.”Footnote 43 Because trust is a necessary condition for defense cooperation, the creation of a DCA functions as a reassuring signal of cooperative intent to observant third parties.
DCAs also increase ex post trust. For example, the defense minister of Iran referred to his country's 2002 DCA with Kuwait as a “trust-building effort,” echoing a phrase that appears repeatedly in leaders’ statements and in the texts of DCAs themselves.Footnote 44 The prime ministers of China and India made this logic explicit in a joint public statement on their 2005 DCA, noting that “broadening and deepening of defense exchanges between the two countries [are] of vital importance in enhancing mutual trust and understanding between the two armed forces.”Footnote 45 DCAs build confidence by repeatedly engaging governments in concrete acts of cooperation that entail nontrivial risks.Footnote 46 While collaboration problems primarily involve issues of ex ante trust, I show later that increased ex post trust amplifies the network effects of DCAs.
Coordination problems are also apparent in DCAs. Variations in the institutional characteristics of DCAs partially reflect distributional concerns. Governments worry about asymmetric gains—that is, the possibility that one's partners will gain more than oneself.Footnote 47 Further, negotiators know that revealing a preference for particular design features may lead others to increase their demands accordingly. Given these incentives, governments anticipate that their interlocutors may not be fully transparent about their treaty preferences. That uncertainty, in turn, increases the risk of bargaining failure. Given their broad flexibility as framework agreements, DCAs particularly raise concerns about scope, precision, and the degree of reliance on implementing arrangements.
A contentious 2007 negotiation between Singapore and Indonesia offers an illuminating example. In response to Singapore's request for access to Indonesian waters for training purposes, the resulting DCA included a seemingly benign implementing arrangement that designated an “Area Bravo” southwest of Indonesia's Natuna Islands.Footnote 48 Almost immediately upon signature of the DCA, Indonesian politicians accused Singapore of disingenuousness and began speculating on the “broad latitude” that the Singapore military would wield in Area Bravo, involving naval exercises, air support, live fire, and even participation of third parties—all of which, given Singapore's growing military strength, would likely intensify over time.Footnote 49 Indonesia's defense minister, seizing on ambiguities within the agreement, declared that “Singapore still wants rules of their own, without having to negotiate … on their military training here.”Footnote 50 He further asserted, “We want clear rules of the game on the frequency and scope of Singapore military training, including how many times Singapore can fire its missiles in our territory.”Footnote 51 While Singapore's true preferences remain opaque, the mere perception of duplicity by the Indonesian government was sufficient to doom the proceedings.
Although joint gains and information asymmetry are complementary principles, they involve distinct causal mechanisms. In the case of joint gains, noncooperation occurs because the gains from cooperation aren't sufficiently large relative to the noncooperative status quo. In the case of information asymmetry, noncooperation occurs because states lack credible information about trustworthiness or institutional design preferences. This distinction allows us to cleanly theorize the causal mechanisms that influence defense cooperation. Joint-gains mechanisms encourage cooperation by shifting the relative payoffs of cooperative and noncooperative outcomes and thus increasing demand, while informational mechanisms encourage cooperation by reducing or eliminating information asymmetries and thus increasing supply.
Exogenous Sources of Defense Cooperation
Demand for DCAs is rooted in a combination of system-level historical contingencies, including the fall of communism, the decline in interstate conflict, and especially the rise of nontraditional threats. These changes are largely global and secular, coming to fruition in the final days of the Cold War. Historical evidence reveals a shift in the language of defense cooperation over the course of the 1980s. In 1981, the US and Israel signed a traditional defense agreement, not a DCA, “designed against the threat to peace and security of the region caused by the Soviet Union or Soviet-controlled forces from outside the region.”Footnote 52 By the time of the Soviet Union's collapse, Israel had grown “anxious to forge a new definition for their partnership with the world's sole superpower.”Footnote 53 Attention shifted toward civil wars in the Balkans, instability in Algeria, missile and nuclear proliferation, and “a mutual interest in keeping the Central Asian states from becoming strongholds of Islamic extremism.”Footnote 54
In the years since, US defense policy has evolved to manage an increasingly complex security environment. US Secretary of Defense Ash Carter recently articulated the need for a “principled security network,” of which bilateral defense agreements are a key component.Footnote 55 This network would address both traditional concerns (for example, “Russian aggression from the east”) and new threats like terrorism, piracy, refugee flows, humanitarian assistance, natural disasters, and cyber warfare.Footnote 56 In short, the new global security environment has increased demand for novel forms of cooperation. Governments do not simply sign DCAs wantonly. States differ in their exposure to novel security threats, and partnerships with some states offer more promise in managing these threats than others. I employ historical accounts to identify three related but analytically distinct pressures on bilateral demand for defense cooperation. Subsequently, I translate these bilateral influences into a series of control variables.
Modernization
Governments increasingly turn to DCAs as a means of improving their military capacity. For example, Bulgaria has waged a modernization campaign since the 1990s, involving dozens of DCAs that, according to US diplomats, are “based on the premise that Bulgaria faces new asymmetrical security threats rather than traditional threats to its national territory.”Footnote 57 In 2011, Indonesia pursued DCAs with a wide swath of partners—including Russia, South Korea, China, Serbia, and India—in an effort to “modernize the country's main armament system.”Footnote 58 Modernization also includes R&D and industrial cooperation. In 2005, Ukraine's defense minister argued that a DCA with Russia would capitalize on the “scientific and industrial potentials of Ukraine and Russia” and enable “co-production arrangements for defense-industry enterprises in the development and production of armaments and military hardware.”Footnote 59 Officer exchanges and training programs comprise yet another source of military capacity. A defense official from the Philippines, following a 2006 agreement with Australia, observed: “It's like a basketball game. We need to practise with other players from other teams to learn new skills and techniques to raise the level of our game.”Footnote 60 The defense minister averred, “In three years, we could raise the military's readiness from 45 percent to 70 percent.”Footnote 61
Common Security Threats
States respond not merely to global threats but to threats shared in common with potential partners. For example, the Grand Mufti of Brunei argued for a DCA with Indonesia by appealing to a sense of shared fate, declaring that “in the future, we will likely face nontraditional threats, which do not recognize state borders. It is thus a must for two neighboring countries to set up military cooperations.”Footnote 62 Indonesia's defense minister explained his country's 2016 DCA with Sweden by stating that “our common enemy is terrorism.”Footnote 63 Although asymmetric threats receive disproportionate attention, leaders also retain concerns about traditional interstate threats. The defense ministers of Iran and Syria described a 2006 DCA as a response to the “common threat” posed by the United States and Israel.Footnote 64 Iran's defense minister similarly declared that a 2005 DCA with Tajikistan would “deter foreign forces who aim to find a foothold in the region on the pretext of restoring security.”Footnote 65
Alignment and Security Communities
Scholars have long argued that states use defense ties to signal affinity with particular collaborators.Footnote 66 A Brazilian military analyst, explaining the 2010 DCA with the US, argued that “Brazil is aligning itself strategically with the US, like the European nations have done with NATO,” while Secretary of Defense Robert Gates described the deal as “a formal acknowledgement of the many security interests and values we share.”Footnote 67 At their most ambitious, alignment efforts coalesce into nascent communities.Footnote 68 Upon signing a DCA with Chile in 2012, the Canadian government reiterated a commitment to “working with like-minded nations to promote peace and security throughout the Americas.”Footnote 69 In 2012, a Philippines senator argued that a DCA with Australia—complementing DCAs with South Korea, Japan, Australia, New Zealand, Singapore, and Indonesia—would finalize a pan-Asian “security umbrella.”Footnote 70 And Secretary Ash Carter's farewell memo describes the above-mentioned principled security network as “open to all that seek to preserve and strengthen the rules and norms that have undergirded regional stability for the past seven decades.”Footnote 71
Combined with cooperation theory, these historical accounts translate into a basket of straightforward empirical expectations. First, demands for modernization imply that, ceteris paribus, cooperation with wealthy, powerful partners offers the greatest prospects for joint gains. As well, countries that are active in the global arms trade should be favored as defense partners, given their ability to supply weapons and materiel.Footnote 72 A caveat to this expectation is that although partnerships with militarily powerful countries are more likely to reap material rewards, mutually powerful countries often view one another as competitors. Thus, military power should increase the probability of DCAs, but only between trusted partners.
Second, when governments face common security threats, whether interstate or nonstate, the joint gains of defense cooperation should increase accordingly. The perception of common threat is a long-standing motivator for defense pacts.Footnote 73 Further, in standard public goods models of alliances, threat level directly determines the utility of, and thus the demand for, defense cooperation.Footnote 74 I anticipate an analogous relationship with DCAs.
Third, the discussion of alignment and security communities implies that joint gains increase when states are politically similar, aligned in their foreign-policy preferences, or otherwise strategically valuable. Accordingly, I expect shared democracy and foreign-policy affinity to increase the probability of DCAs.Footnote 75 Further, because international trade reflects strategic economic interests,Footnote 76 I expect bilateral trade to encourage DCAs.
Fourth, traditional military alliances exercise influence in a variety of ways. Allied countries are better equipped to meet one another's modernization needs, more likely to face common threats, and more likely to share foreign-policy goals. Thus, alliances should generally increase demand for DCAs. However, I anticipate a unique influence for NATO because its unusually broad mandate spills into issue areas—training, defense research, joint exercises, etc.—also addressed by DCAs. Accordingly, demand for DCAs should be lower between NATO states. At the same time, because DCAs are an important mechanism for prospective NATO members to signal alignment, I anticipate a positive effect for pairings between NATO members and Partnership-for-Peace (PfP) states.
Defense Cooperation and Network Influence
Exogenously motivated demands for defense cooperation, though important, do not explain how states have managed to overcome the information asymmetries that plague cooperative efforts. While some powerful, wealthy governments may be willing to risk cooperation despite uncertainty, DCAs have proliferated far beyond the powerful and wealthy. Even former adversaries like Australia and Indonesia, Brazil and Argentina, and Ukraine and Russia have now signed DCAs. I argue that when states sign DCAs, they reveal information about their trustworthiness and design preferences to third-party observers, and those revelations in turn drive empirically observable network influences. As the density of the DCA network increases, network influences multiply. Information about the trustworthiness and institutional design preferences of prospective partners becomes more readily available, thus increasing the supply of agreements. Importantly, network influences are not merely supplementary. Post-Cold War, they are in fact the primary determinants of new DCAs.
I thus operationalize DCAs as a global network, where a network is simply a collection of “nodes” (that is, countries) connected to one another via “edges” (that is, DCAs), and where the edges, though separable, are not independent of one another. The probability of a tie between a given i and j is then endogenous to the probability of a tie between i and k, or k and j, or k and l, and so on. Figure 4 illustrates the DCA network in Asia in 2010. As a network, the probability of any given edge is a function, in part, of other edges in the network, which defines the phenomenon of network influence. Conditional on the various exogenous influences discussed previously, the probability of a DCA between a given i and j depends on who else has signed DCAs.

Figure 4. Defense cooperation network in Asia, 2001–2010
In theorizing network influences, I focus on the capacity of DCA creation itself to signal information to observant third parties. I emphasize DCA creation—rather than compliance with DCAs over time—for three reasons. First, although DCAs often incorporate “trust-building” measures, ex ante trust remains a necessary condition. Second, even if compliance increases ex post trust, these effects may not be measurable. Some DCA activities—sharing of classified information, joint military research, defense policy coordination—are difficult to observe. Third, DCAs reveal information about scope, depth, and other institutional design issues immediately upon signature, regardless of compliance. Nonetheless, I later identify areas where ex post trust, generated by observed compliance, further strengthens network influences, particularly when mediators are involved.
Network influences take many forms. I focus on two, preferential attachment and triadic closure, which together characterize an enormous variety of natural, social, and physical networks.Footnote 77
Preferential Attachment
In a generic preferential attachment process, highly popular actors or “hubs” attract additional network ties because of their large number of existing ties.Footnote 78 Figure 5(a) illustrates this process, where the relative attractiveness of a potential target depends on its total number of ties or nodal degree centrality. High-degree nodes (j 1) are more likely to attract new ties than are low-degree nodes (j 2). In the context of the DCA network, preferential attachment means that states favor partners that have large numbers of agreements in place. Thus, the probability of a given ij tie is endogenous to the ties in place between j and its various k partners.

Figure 5. Two network influences
The fundamental insight of preferential attachment is that states favor high-degree nodes not because those nodes are more powerful, wealthy, or democratic, but precisely because they are high-degree nodes. Empirical assessment of preferential attachment thus requires careful attention to correlated influences, while theoretical explanations require careful arguments for why states prefer ties to high-degree nodes. In the case of DCAs, preferential attachment directly reflects an informational mechanism, involving both trustworthiness and institutional design.
First, ceteris paribus, states that accede to large numbers of defense agreements signal diffuse trustworthiness.Footnote 79 The informational quality of this signal depends, in part, on the costs incurred by high-degree nodes.Footnote 80 DCAs involve nontrivial transaction costs. Some DCAs take years to negotiate. Most require implementing legislation, which carries a risk of opposition from domestic factions. Once implemented, DCAs necessitate maintenance costs, such as joint working groups, defense industrial collaboration, and educational exchanges. The most substantial cost is the risk of failure. Sharing classified information with, collaborating in defense research with, or exporting weapons to an untrustworthy state does not enhance security but undermines it. These risks define the collaboration problem in DCAs. Importantly, governments recognize that DCA commitments reassure others of one's benign intentions. In 2008, for example, the US embassy in Jakarta observed that “signing a DCA with Indonesia would send a strong message of mutual trust” and “create a firmer basis for mil-mil cooperation.”Footnote 81 Similarly, Secretary Carter described the many US bilateral defense agreements in Asia as “confidence-building measures” and “effort[s] to improve transparency.”Footnote 82 All else equal, a willingness to accept the risks of DCAs on a broad scale constitutes a “public commitment” to cooperative over exploitative policies,Footnote 83 which in turn makes high-degree nodes more attractive partners.
Second, high-degree nodes reveal strategically valuable information about the types of agreements they are willing to sign, which may involve questions of issue-area scope and precision of legal obligations. This information mollifies concerns about duplicity and clarifies the range of mutually acceptable bargains, which effectively lowers the transaction costs of cooperation and simplifies bargaining over distributional outcomes. Political economists argue that early US PTAs were “bellwethers” that communicated US trade preferences to subsequent partners.Footnote 84 DCAs work analogously. Following a DCA with Australia in 2006, the defense minister of the Philippines argued that the agreement functioned as “a template for similar arrangements with Southeast Asian states, such as Brunei, Indonesia, Malaysia and Singapore.”Footnote 85 As anticipated, the Philippines later cited this DCA in negotiations with Singapore and others.Footnote 86 France invoked similar logic during its expansion of defense cooperation into Latin America. In 2002, as the French government pushed its legislature for ratification of a DCA with Argentina, the prime and foreign ministers issued a joint statement declaring: “The agreement provides good visibility to our bilateral defense relations and acts as a model for the conclusion of similar agreements with many partners in the region.”Footnote 87 This prognostication proved correct. France shortly thereafter signed DCAs with Venezuela, Peru, and Brazil.
Because high-degree states reveal valuable information about their trustworthiness and about the types of agreements they are willing to sign, cooperation with such partners, ceteris paribus, poses fewer coordination and collaboration problems. This informational mechanism generates an observable preferential attachment effect.
H1
States are more likely to sign DCAs with partners that sign large numbers of DCAs themselves.
Triadic Closure
In some contexts, degree centrality may not be a sufficiently credible source of information. For example, many Eastern Bloc countries were high-degree nodes, but this fact likely did not convince potential partners of their trustworthiness.Footnote 88 I further hypothesize, then, that states favor ties to partners of partners or “friends of friends.” Such dynamics typically involve some form of transitivity, such as triadic closure, wherein nodes form closed triangles in their network relations.Footnote 89 Closure is best illustrated, as in Figure 5(b), by an unclosed or “forbidden” triad, where a preference for closure encourages the formation of a crucially missing third tie. The greater the number of third-party ties between i and j, the stronger the pressure for closure.
In DCA networks, triadic closure means that i and j are more likely to cooperate if they both sign DCAs with a common k third party. As with preferential attachment, this network influence depends on informational mechanisms. If trust is not diffuse but is instead specific to bilateral relationships,Footnote 90 then a country's myriad DCA ties cannot credibly inform others of its trustworthiness unless those ties hold relevance for potential partners. Figure 5(b) shows how the presence of multiple k partners between i and j 1 allows those k third parties to “mediate” the signals generated by i and j 1’s respective DCAs. In signing a DCA with k, i incurs costs, rooted in the inherent risks of defense cooperation. Those costs in turn signal reassurance to k’s partners, including j 1. The crucial element that makes the ik DCA informative for j 1 is the DCA between k and j 1. As k’s partner, j 1 is immediately familiar with k’s risk propensity, its standards in evaluating defense partners, and its expectations for mutual collaboration—pieces of information that, if j 1 were simply a disconnected bystander like j 2, would be more difficult to access. Thus, k’s agreement with i is both a costly and a confirmatory signal.Footnote 91 Not only does j 1 observe that i is willing to risk cooperation, but j 1 further observes that its own trusted defense partners have confirmed i’s trustworthiness.Footnote 92
Historically, states have attempted to signal reassurance to partners of partners in precisely this way. In 1997, Romania declared it would “boost [its] chances of early admission to NATO by developing a new partnership with Hungary,” clearly anticipating that Hungary's willingness to sign an agreement would reassure Hungary's partners—NATO member states—of Romania's cooperative intentions.Footnote 93 The Estonian defense minister similarly described a DCA with Turkey as a way “to show its good relations with all members of the [NATO] alliance,” with the hope that approval from Turkey would translate into approval from Turkey's partners.Footnote 94 And in 1998, Ukraine signed an extensive DCA with Argentina in part to reassure Argentina's defense partners, particularly the United States, of Ukraine's interest in cooperation with the west.Footnote 95
Yet, third parties are not limited to acting as passive bystanders. Even if k separately trusts both i and j, a challenging information environment may limit diffusion of trust. This gap creates an opportunity for the k third party to exercise initiative.Footnote 96 Kydd observes that if a “mediator is to build trust between the parties, it must have some information to share with them about the other side's type.”Footnote 97 At the same time, third parties often support increased cooperation between their defense partners because trilateral DCA arrangements facilitate interoperability, information sharing, and coordinated responses to mutual threats.Footnote 98 Having “something to gain” from ij cooperation is in fact essential to k’s ability to provide credible information.Footnote 99 Combining these elements, k’s direct ties to i and j provide k with credible information about each state's trustworthiness, and the prospect of enhanced trilateral cooperation incentivizes k to actively use that information to promote an ij tie. Importantly, this logic integrates the ex post trust discussed earlier. If k has first-hand evidence of long-term compliance in its relations with i and j—and thus high ex post trust with respect to both—this improves k’s ability to build ex ante trust between them.
The complex defense relationship between Japan and South Korea, with the United States as the k mediator, illustrates this logic.Footnote 100 A Japanese military analyst noted, “Japan and South Korea indirectly cooperate with each other via the US currently. If the two nations directly work together, this would reduce the US burden.”Footnote 101 For example, a direct Japan-Korea DCA would allow Japan's signal intelligence to complement South Korea's substantial human intelligence, ultimately improving the capacity of all three governments to meet the North Korean nuclear threat. Analysts and US defense officials agree that all sides would benefit from “completing the triangle.”Footnote 102 Yet an agreement remains elusive, almost entirely because of lingering mistrust. Accordingly, the US has acted as an “honest broker” and pursued numerous trust-building measures,Footnote 103 including sideline talks at multilateral events, the annual Defense Trilateral Talk, and small-scale “tabletop” exercises, as well as tentative extensions into interoperability, logistics, and supply.Footnote 104 The success of these actions depends upon the mediator's ability to credibly inform each side of the other's trustworthiness.
These arguments lead to the following hypothesis:
H2
States are more likely to sign DCAs with the DCA partners of their own DCA partners.
Mechanisms of Network Influence
Is there empirical evidence of preferential attachment and triadic closure in DCAs? Figure 6 uses hive plots to illustrate the topology of the DCA network. The left-hand panel shows the full network, with gray edges representing DCAs and nodes representing countries, organized by region. Nodal degree refers to each country's number of signed DCAs. In the middle panel, edge shading reflects the mutual degree of DCA partners, or the average of i and j’s nodal degree scores. The abundant dark-shaded edges indicate a tendency toward partnerships with high-degree nodes, consistent with the logic of preferential attachment. To emphasize triadic closure, the right-hand panel shows only those ties that are part of at least one closed triangle, where edge shading reflects the number of third-party ties or two-paths between a given pair of nodes. The density of this subgraph suggests that closure is very common in the DCA network. Over half of ties are part of at least one closed triangle. The topology of the DCA network thus shows evidence of both preferential attachment and closure.
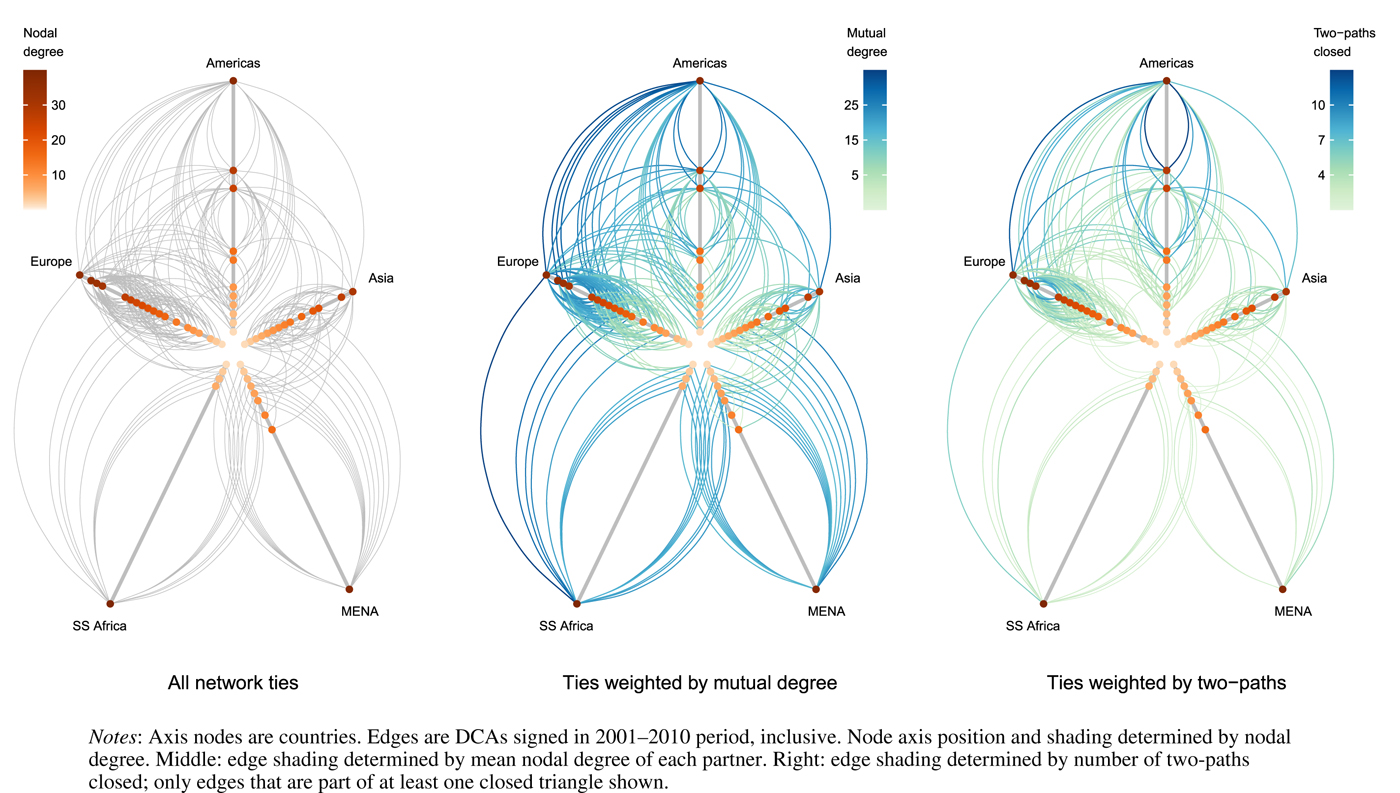
Figure 6. Topology of bilateral DCA network in hive plots
If preferential attachment and triadic closure encourage DCAs, we should also observe that these mutual degree and two-paths statistics are larger for states that sign DCAs than for the full population of states.Footnote 105 Figure 7 illustrates the distributions of these two statistics first for all dyads and then for the subset of dyads that have signed at least one DCA. In the full population, mean mutual degree hovers around zero. For those dyads with at least one DCA, the mean increases to about seven. For two-paths, in the full population over 90 percent of dyads share no third-party ties at all. For countries with at least one DCA, nearly 60 perent of dyads share ties to at least one third party. If DCAs were truly independent events, the probability of i and j signing a DCA would not be strongly correlated with their ties to third parties, and the distributions in Figure 7 would be similar across samples.

Figure 7. Distributions of mutual degree and two-paths across samples
Figures 6 and 7 nonetheless say little about mechanisms. The most plausible alternative to the proposed informational mechanism is that network influences are in fact driven by joint gains. For example, a country's nodal degree may be epiphenomenal to the size of its defense industry or to some other attractive attribute. Relatedly, network ties may generate externalities that incentivize further cooperation, a phenomenon found in other international relations networks.Footnote 106
Fully accounting for these possibilities requires careful attention to research design. Here, I propose a novel empirical strategy for testing the informational mechanism. Crucially, I assume that the informational content of network ties is most valuable prior to i and j’s first DCA. Network ties convey information credibly but indirectly. Once states sign a DCA, they subsequently establish joint working groups, compose annual plans, exchange officers, hold joint exercises, participate in defense research projects, conduct peacekeeping operations, exchange classified information, and so on. These activities build ex post trust. Further, as a result of negotiating the DCA, they have first-hand knowledge of one another's institutional design preferences. Thus, with a DCA in force, the need for third-party sources of information declines.
This insight has found support elsewhere. Using an agent-based model, Jung and Lake show that network ties allow agents to gather valuable information about potential partners and increase the probability of cooperation; but once cooperation occurs, those ties no longer provide novel information, and their influence dissipates.Footnote 107 Fafchamps, Leij, and Goyal find that network ties encourage first-time coauthorships among economists but have no effect on subsequent collaborations.Footnote 108 If network influences depend on an informational mechanism, then those influences should most strongly affect i and j’s first DCA and should weaken for subsequent DCAs. By contrast, if network influences depend on other mechanisms, such as joint gains, they should persist even after the first DCA. For example, if partnerships with high-degree nodes simply offer greater utility—say, because those nodes have reaped the benefits of myriad defense ties—then a high-degree j’s attractiveness as a defense partner should affect not only i’s first agreement with j but also subsequent agreements; a rational i will attempt to leverage joint gains regardless of when agreements are signed. The next section further elaborates on this logic and on the proposed placebo-like test.Footnote 109 For now, I hypothesize:
H3
If network influences depend on informational mechanisms, those influences should be strongest for the first DCA and weaker for subsequent DCAs.
A related implication of the informational mechanism is that if states have access to high-quality sources of direct information beyond the DCA network, then network influences should matter less. Specifically, when states exchange high-level diplomatic corps, or share memberships in highly structured intergovernmental organizations, or cooperate in institutionalized military alliances, they already possess direct avenues for communicating trustworthiness and institutional design preferences. Third-party network ties may still matter in such cases, given that they convey information specifically about DCA-related preferences, but they should matter less. Thus, I hypothesize:
H4
If network influences depend on informational mechanisms, those influences should weaken for dyads that have access to alternative sources of information.
Exogenous Versus Network Influences
These network influences complement the exogenous influences discussed previously. Nonetheless, given that exogenous influences initially stimulate demand for defense cooperation, they are historically prior to network influences. At what point in the history of DCAs do network influences become substantively important? In the waning days of the Cold War, defense cooperation largely reflected geopolitical contests between wealthy, economically integrated major powers since these governments stood to gain the most from defense cooperation and also possessed the resources to extend risky cooperative overtures.Footnote 110 As the Cold War faded, the interests of major powers shifted from interstate concerns toward nontraditional security threats.Footnote 111 Other governments, no longer ensconced in stark regional blocs, quickly recognized their vulnerability to these same threats. The growing potential for joint gains crystallized a broad interest in decentralized systems of defense cooperation.Footnote 112 However, in contrast to the emergence of DCAs in the 1980s, this interest in defense cooperation was not limited to major powers and their immediate partners but encompassed middling, minor, and regional players. These governments, lacking the major powers’ capacity to absorb risk and cover the costs of governance, required stronger assurances of trustworthiness from their prospective partners. The existing network of DCAs, forged between major-power hubs and their satellites, offered an important resource, providing crucial information on the preferences of potential partners. Overall, then, the “first movers” in DCA creation should be wealthy, powerful, economically integrated governments. As the Cold War fades and other governments—recognizing the need for security cooperation but lacking the major powers’ resources—begin to show an interest in decentralized defense cooperation, network influences should grow in strength.
H5
During the Cold War, DCAs are largely determined by exogenous influences, while network influences emerge post-Cold War.
Research Design
The nature of the DCA data, combined with the causal questions raised by the hypotheses, pose unique estimation problems. Because network data violate the assumption of independently distributed observations, many scholars recommend inferential network models, such as exponential random graph models (ERGMs).Footnote 113 However, network models require complete N × N matrices of data, which prevents implementation of the split samples required to test the informational mechanism. I instead follow the approach of Fafchamps, Leij, and Goyal and estimate a series of carefully specified fixed-effects logistic regression models.Footnote 114 Nonetheless, as the appendix shows, I subjected the DCA data to multiple inferential network models, and the results universally support the main network hypotheses while also producing comparable estimates of the exogenous influences.
My preferred model consists of three elements. First, to account for time-invariant sources of unobserved heterogeneity, I include pairwise (that is, dyadic) fixed effects (FEs), which are crucial to causal inference. A country's DCA activity may be correlated with fixed attributes of that country, such as geopolitical position or other material determinants of power and prestige. FEs are a simple but powerful means of ensuring that such attributes do not confound inference. FEs can also account for many immaterial influences, such as a reputation for strength or military quality, because reputations in IR tend to be slow moving.Footnote 115 In short, the FEs absorb a wide variety of potentially confounding influences. Second, to account for known time-varying effects, I include a series of control variables, derived from the discussion of exogenous influences.
Third, I conduct placebo-like tests, estimating the FE model on two samples: dyads that have signed at least one DCA, and dyads that have signed no DCAs.Footnote 116 This specification not only tests H3 but also accounts for the possibility that, despite the controls, excluded time-varying influences may be correlated with the network influences. Consider the example of a state that improves in military quality over time. Following the logic of joint gains, this improvement should make that state a more attractive DCA partner. If military quality correlates with degree centrality or third-party ties but is omitted from the model, parameter estimates may be biased. However, any time-varying influence on joint gains should be just as influential on subsequent agreements as on a first agreement since there is no plausible reason that countries interested in powerful, wealthy, similarly aligned, or otherwise strategically valuable partners should suddenly lose interest once a first agreement has been signed. Thus, if the network influences are spurious to such excluded time-varying influences, we would observe, contrary to expectations, that their effects do not differ between the placebo and treatment groups. On the other hand, if network influences derive, as hypothesized, from informational mechanisms, they should differ significantly in magnitude between the two groups. Combined with the FEs, this specification is thus a powerful tool for improving causal inference.
This approach yields two estimating equations:
and
In both cases, y ij,t is a binary indicator of whether i and j sign a DCA in year t; α ij is a measure of triadic closure; γ ij is a measure of preferential attachment; δ ij represents exogenous dyadic and monadic influences; and μ ij represents dyadic fixed effects. To avoid simultaneity bias, I lag all regressors, including the network terms, by one year. This specification also requires linear detrending of the regressors to further reduce the risk of spurious correlation,Footnote 117 and it assumes that the network terms influence the outcome with at least a one-year lag. The appendix discusses these modeling choices in further detail.
Because DCAs are nondirected, all variables must enter these equations symmetrically. I operationalize the α ij and γ ij terms by calculating a two-paths variable and a mutual degree variable, respectively. Two-paths is the log-transformed dyad-year count of the number of third parties with whom i and j mutually signed DCAs in the prior five years. Mutual degree is the log-transformed dyad-year mean of the total DCAs signed by i and j in the prior five years. The appendix explores a number of alternative specifications and also shows that varying the five-year window has no substantive impact on the results.
I also include a series of additional variables to control for exogenous influences, each of which, like the network terms, must enter the estimating equations symmetrically. To control for modernization demands, I include mean power, the mean of i and j’s log-transformed CINC scores; mean gdp/capita, the mean of i and j’s log-transformed GDPs; and arms match, a dummy variable that equals 1 if i or j is an arms exporter while the other is an importer. To control for common security threats, I include mutual enemy, a count of i and j’s MIDs against common third parties in the past five years; and mutual terrorist threat, the mean of annual fatal terrorist attacks by foreigners in i and j. To control for the influence of political alignment, I include mutual democracy, a dummy variable that equals 1 if i and j are both democracies; unga ideal point diff, representing the difference in policy positions between i and j in the United Nations General Assembly; and bilateral trade, the log-transformed volume of bilateral ij trade flows. Finally, to control for alliances, I include dummy variables for NATO membership, non-NATO defense pacts, and joint NATO-PfP pairings. The pooled logit model also includes geographic distance and a dummy for prior colonial ties, both of which drop out of the FE models. The appendix provides sources for each of these measures and considers alternative operationalizations.
Empirical Analysis
I first estimate a pooled logit model with standard errors clustered on dyads for the entire 1980–2010 period. Figure 8 illustrates the results. Regarding exogenous influences, the results are mixed. Arms match and mean gdp/capita are both positively associated with DCAs, but the estimates are just shy of significance. Mean power appears to increase defense cooperation unconditionally (that is, regardless of existing levels of trust). Further, the estimates for both mutual enemy and mutual terrorist threat are insignificant. Expectations regarding political alignment, on the other hand, are strongly supported. Mutual democracy and bilateral trade both significantly increase the probability of a DCA, while divergences in UNGA voting positions reduce that probability. I also find that defense pacts make DCAs more likely while joint NATO membership makes them less likely. NATO-PfP pairings, contrary to expectations, have no effect.
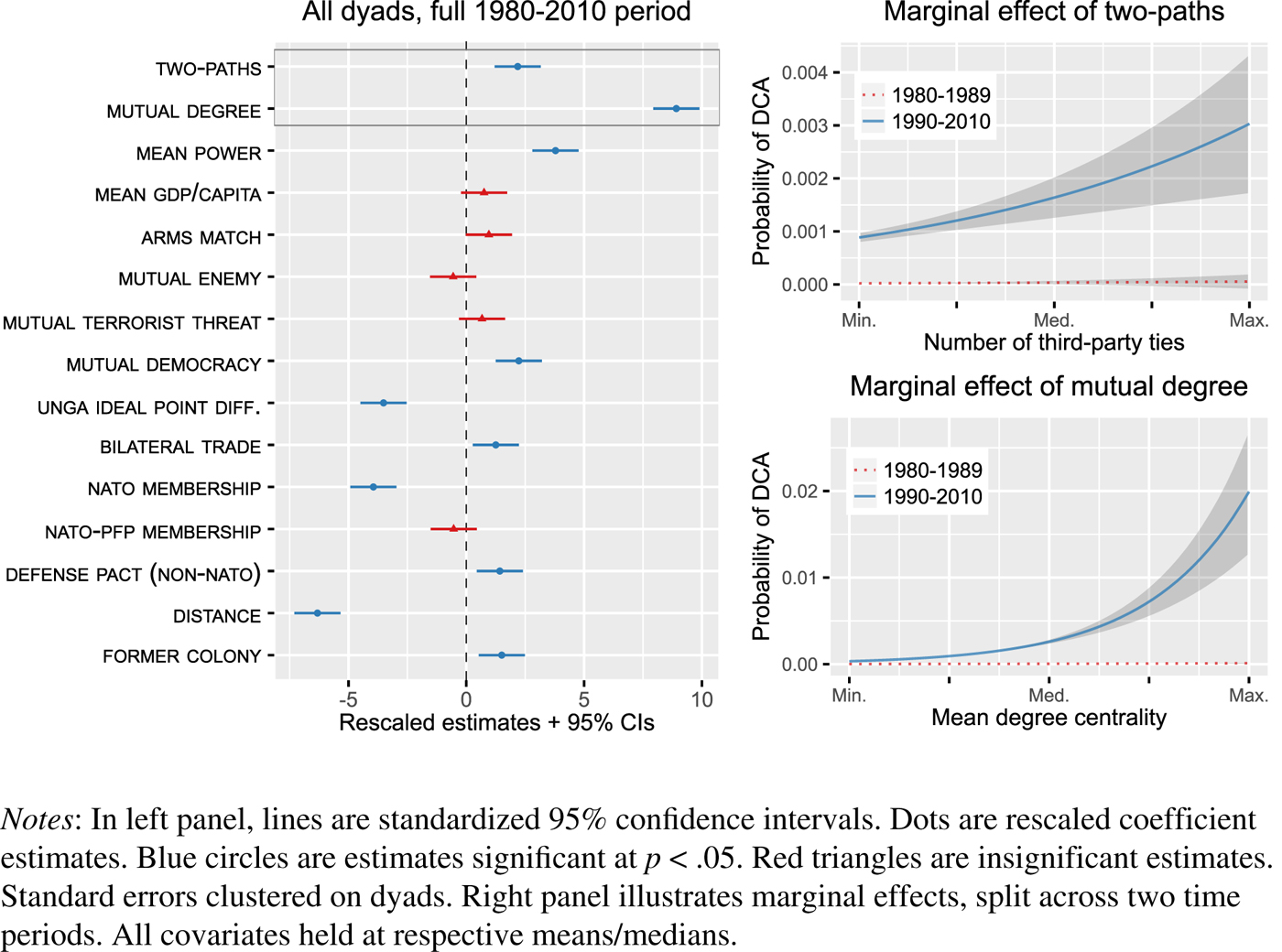
Figure 8. Pooled logit estimates and marginal effects, 1980–2010
The estimates for mutual degree and two-paths are positive and extremely precise, providing initial support for H1 and H2, the key network hypotheses. Dyads that share DCA ties to the same k third parties are more likely to sign DCAs themselves. Further, as the centrality of i and j in the DCA network mutually increases, their probability of signing a DCA increases correspondingly. This last result suggests that, conditional on military power and other covariates, cooperation is most likely between mutually active countries, where information provision is greatest. To assess H5's macro-historical argument on the emergence of network influences, I calculated the marginal effects of the network variables separately for the 1980–1989 and 1990–2010 periods. As the right-hand panels in Figure 8 show, when DCAs first emerged in the 1980s, network influences were virtually nonexistent; separately estimated models reveal that, during this period, military power and bilateral trade are in fact the main determinants of defense cooperation. These findings are consistent with the structural argument that network influences only became important as traditional geopolitical concerns waned, novel threats emerged, and a diverse array of states found themselves in need of bilateral defense partners.
The pooled model cannot address unobserved heterogeneity and, most importantly, does not provide sufficient leverage to test the causal claim that network influences encourage DCAs by disseminating information. I thus turn to the fixed-effects estimator, combined with placebo-like tests, estimated on the 1990–2010 period. Figure 9 illustrates the estimates. The left-hand panel corresponds to Equation 1 (that is, the “first agreement” equation). Consistent with the initial findings from the pooled model, both mutual degree and two-paths strongly encourage DCA cooperation, and both estimates are very precise. Interestingly, the estimates for many of the control variables have shifted. The estimate for mean power has flipped signs and is now strongly negative, which accords with the expectation that mutual power discourages cooperation when trust is low. At the same time, mutual wealth now greatly increases DCA cooperation, as anticipated. The estimate for mutual enemy is also significantly positive, indicating that as dyads face increased common threats over time, they are more likely to sign DCAs. Nato-pfp membership is also positively and strongly associated with DCAs. Overall, the FE model yields estimates that closely align with expectations.

Figure 9. Fixed-effects logit estimates of new DCA ties, 1990–2010
The right-hand panel of Figure 9 shows that, for the sample of dyads that have signed at least one prior DCA, the estimates for the network variables shift dramatically. The two-paths estimate remains positive but is now insignificant, while the estimated effect of mutual degree is now significantly negative. This negative estimate, which is not anticipated by the theory, may stem from diplomatic limitations; that is, highly active countries may lack the resources to negotiate new ij DCAs. Alternatively, high-degree states, given their experience, may simply craft agreements that are less likely to require replacement.Footnote 118 In any case, as I show momentarily, the substantive effect of this estimate is small. I also find a positive estimate for mean power, which, combined with the result for countries with no prior DCA, reinforces the expectation that once countries have established trust via a first DCA, they pursue cooperation with powerful partners. I obtain an unexpectedly negative estimate for arms match in this equation; however, as shown in the appendix, this result is sensitive to operationalization.
Overall, the FE estimates strongly support the hypotheses, including the proposed causal mechanism. Not only do network influences drive DCA formation, but these influences disappear for dyads with existing DCAs. Figure 10 plots the predictive margins for the network variables across the two samples, based on the estimates shown in Figure 9. For low values of mutual degree, the probability of countries signing a first DCA is virtually zero. By the time mutual degree reaches its median value, the probability of a first DCA is nearly 75 percent. Yet for subsequent agreements, denoted by the dashed (red) line, mutual degree is all but irrelevant. Two-paths exhibits a similarly dramatic effect. At the minimum value of two-paths, the probability of a first DCA hovers around 25 percent. By the time two-paths reaches its median value, this probability increases to nearly 75 percent. And as with mutual degree, the effect of two-paths on subsequent agreements is effectively zero. These substantive predictions reinforce the conclusion that network influences depend on informational mechanisms and are not spurious to omitted variables.

Figure 10. Marginal effects of mutual degree and two-paths across samples
As a final consideration of causal mechanisms, I turn to H4. If states have direct means of obtaining information about a potential partner's preferences, they should rely less on third-party sources. I consider four potential direct sources: (1) ambassadorial ties, which allow governments to exchange information via diplomatic corps, military attachés, and possibly espionage; (2) memberships in intergovernmental organizations (IGOs), which allow governments to exchange information via ministers in institutional forums; (3) memberships in highly structured IGOs, which may enhance the credibility of information; and (4) highly institutionalized military alliances, which require some degree of contact, integrated command, joint troop placements, or other mechanisms that increase trust. The appendix details operationalization and data sources.
I interact each of these measures with the network terms in a series of separately estimated models. To simplify interpretation of the interactions, I use the pooled logit model with clustered standard errors.Footnote 119 The embedded forest plots in Figure 11 show the relevant parameter estimates. In all eight cases, the estimated interaction between the network measure and the information measure is significantly negative; that is, as the bilateral information environment improves, the network influences decline in magnitude. Notably, the estimates for the constituent network terms remain positive and highly significant, confirming that when the corresponding information measures equal 0, the network influences are especially important. The marginal effects plots illustrate the impact of network influences for different values of the information measures. For example, the top-left plot reveals that for dyads that fall at the ninetieth centile on the shared IGO membership measure, the effect of two-paths is small. In contrast, when the IGO measure is at the tenth centile, increasing two-paths from its minimum to its maximum increases the probability of a DCA by nearly 400 percent. Overall, the results strongly support the informational story. If states share membership in many IGOs, exchange ambassadors, or jointly participate in an institutionalized alliance, they rely less upon third-party sources of information.

Figure 11. Interaction effects and testable implications of informational mechanism
Value-Added of the Network Approach
Both preferential attachment and triadic closure encourage new DCAs. However, as the theory and empirical results show, exogenous influences also play a role. How much additional explanatory power do the network variables provide? The theory argues that even if exogenous factors increase demand for DCAs, asymmetric information may suppress supply. A crucial test, then, is to determine whether network influences explain outcomes that cannot be explained by exogenous influences alone. I thus compare the out-of-sample predictive performance of the full network model to a model that includes only exogenous covariates. First, I created a training set by randomly selecting, without replacement, half of the dyads in the sample.Footnote 120 Second, using this random sample, I re-estimated the FE model in the left-hand panel of Figure 9, and I also estimated the same model with the mutual degree and two-paths terms excluded. Third, I used the results from the two estimations to generate out-of-sample predictions for the other half of the dyads—that is, the validation set. I repeated this procedure ten times and collected the predictions.
Figure 12 uses receiver operating characteristic (ROC) and precision-recall (PR) curves to illustrate the results. A ROC curve plots the true positive rate of the model's predictions against the false positive rate while gradually increasing the prediction threshold. A larger area under the curve (AUC)—that is, a curve that pushes toward the upper left of the graph—indicates that the model maximizes true positives and minimizes false positives. In this case, the inclusion of mutual degree and two-paths increases the AUC from 0.9 to 0.93. Put differently, the network variables substantively improve our ability to predict exactly when countries sign DCAs. Because these predictions are strictly out of sample (conditional on dyads having signed at least one DCA), they are not artifacts of overfitting.
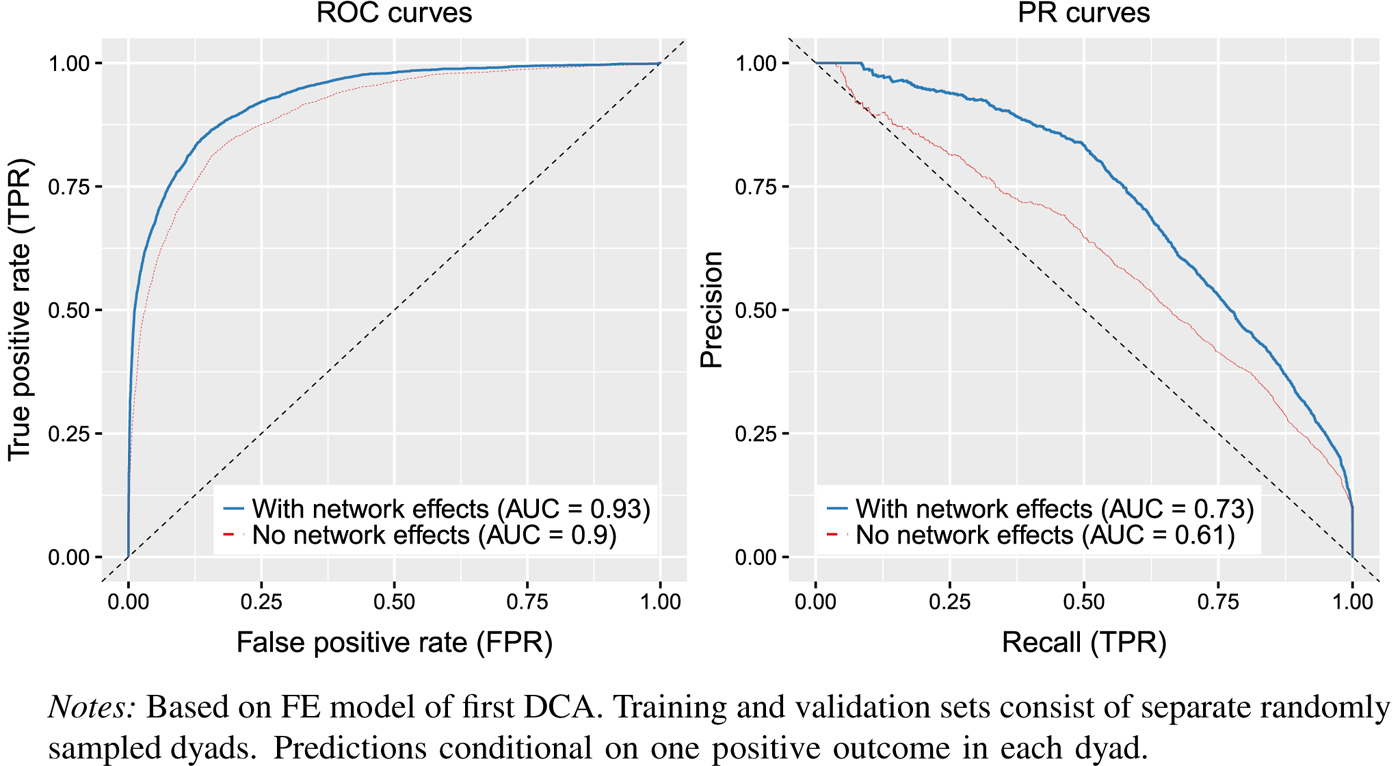
Figure 12. Out-of-sample predictive performance, network vs non-network model
The PR curves in the right-hand panel of Figure 12 show even stronger performance for the network model. As with most IR phenomena, DCAs are relatively rare events. ROC curves may therefore be misleading; a well-fitting ROC curve may be an artifact of how easy it is to predict zeros. The PR curve swaps the false positive rate for precision, which is simply the fraction of the model's predicted DCAs that are in fact correct. As the figure indicates, the network model increases the AUC of the PR curve from 0.61 to 0.73, a nearly 20 percent improvement in fit. In fact, using a prediction threshold of 0.5, the model without network effects successfully predicts only about 35 percent of new DCAs, while the network model predicts over 50 percent. Figure 13 illustrates this difference by plotting, for each country, the number of true DCAs correctly predicted by the network model but incorrectly predicted by the non-network model. Ignoring the role of network ties vastly underestimates the true scope of DCA proliferation. The number of DCAs missed by the non-network model—but correctly predicted by the network model—is well over one hundred. Again, because these predictions are strictly out of sample, they are substantively meaningful and not statistical artifacts.
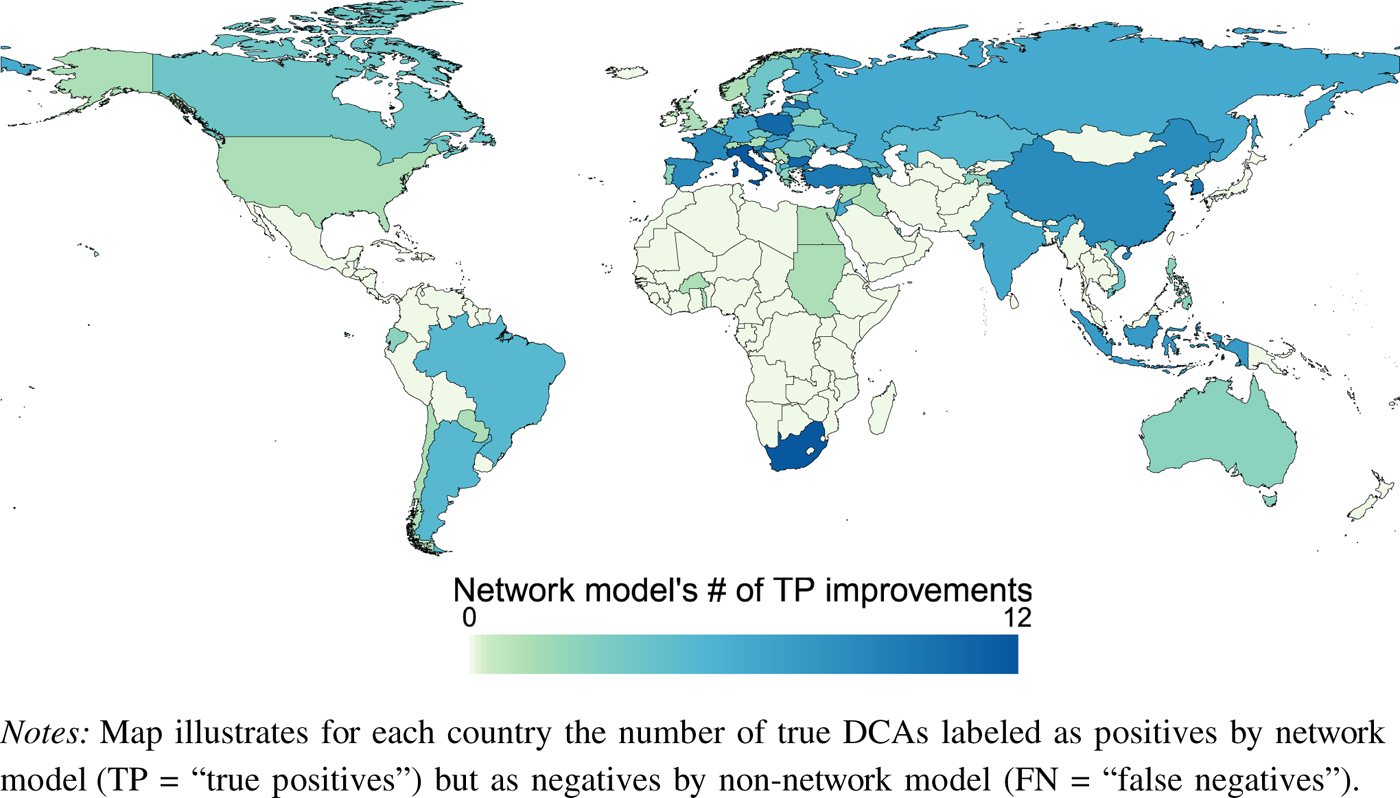
Figure 13. Network model better predicts new DCAs
Finally, I calculated the differences between the out-of-sample predictions generated by the network model and the non-network model, and I isolated those observations where the two models most strongly disagree. The left-hand panel of Figure 14 displays those observations where the network model's positive predictions most disagree with the non-network model's predictions, and the right-hand panel displays those observations where the non-network model's positive predictions most disagree with the network model's predictions. These outcomes represent each model's “hard cases.” In all ten cases where the network model predicts a tie, a DCA was in fact signed. This includes a number of cases that seem difficult to predict, such as Australia (AUS) and Finland (FIN) in 1994, or Netherlands (NTH) and South Korea (ROK) in 1996. By contrast, only three of the ten cases where the non-network model predicts a tie in fact yield DCAs. Not only does the network model outperform the non-network approach in general, but it performs dramatically better in those hard cases where the two models strongly disagree.
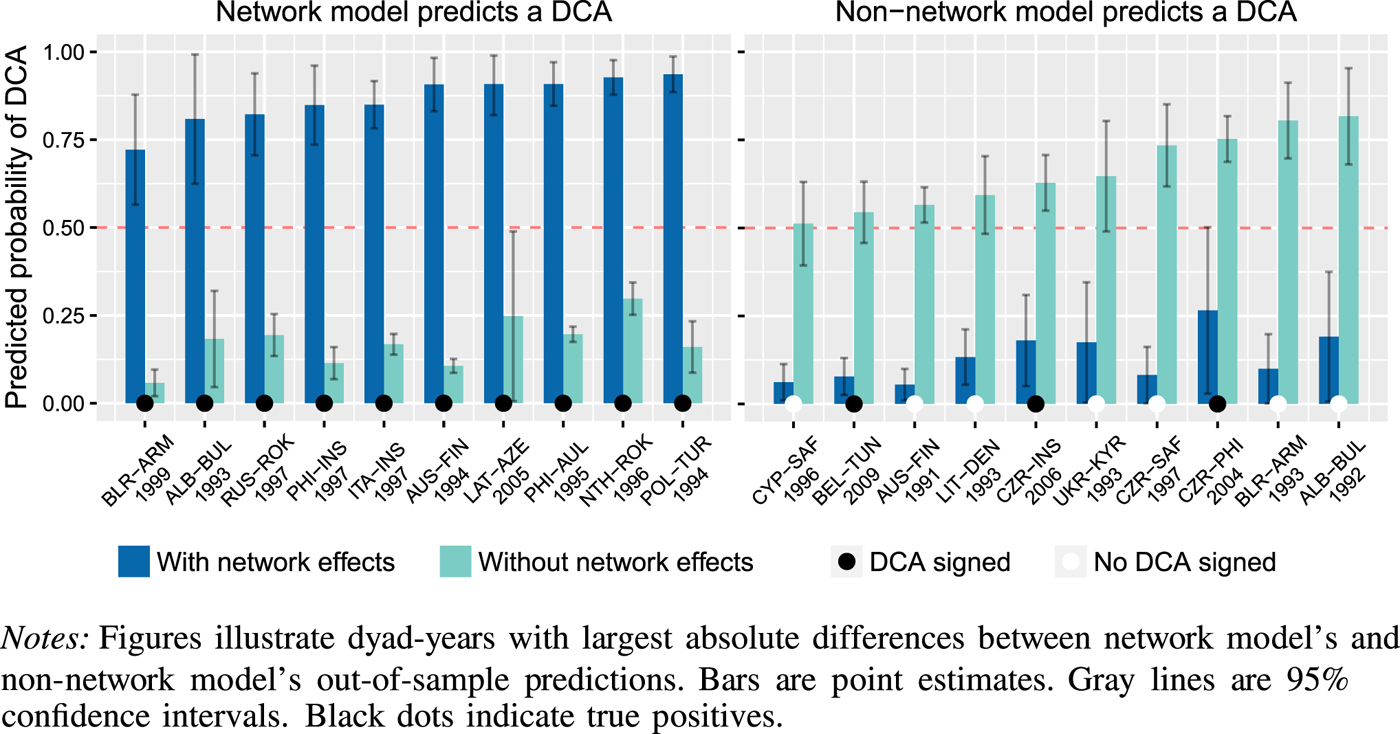
Figure 14. Greatest divergences in out-of-sample predictions
Conclusion
Defense cooperation agreements are an exciting new phenomenon. Nearly as many countries now participate in DCAs as in traditional military alliances. The shifting global security environment has generated demand for new forms of defense cooperation. However, states continue to face long-standing cooperation problems, such as informational asymmetries and distributional conflicts, which dampen willingness to cooperate and lead to an undersupply of defense agreements. A comprehensive approach to DCAs reinforces the important role of exogenous security influences while also emphasizing the importance of network influences. The DCA network helps to endogenously alleviate cooperation problems and encourage otherwise chary states to sign agreements. In-depth empirical analysis shows not only that these network effects are key drivers of defense cooperation, but that the network effects themselves likely derive from informational mechanisms. States respond to the ties of others precisely because those ties reveal strategically valuable information about trust, reliability, and institutional design preferences.
The study of DCAs promises fruitful insights on contemporary internatonal security. I consider three avenues of future research to be especially promising. First, the substantive impact of DCAs deserves consideration. Voluminous anecdotal evidence shows that governments take DCAs very seriously—an insight reinforced by the dramatic proliferation of DCAs over the past two decades. And DCAs often espouse ambitious goals, such as the coordination of the entirety of their respective signatories’ defense relations. Yet we know relatively little about how DCAs accomplish these goals. Figure 2 shows that the potential impact of DCAs is wide ranging, involving arms trade, defense spending, joint military exercises, training and exchange, and militarized conflicts.
Second, variation in the scope of DCAs raises questions of institutional design. In some cases, states assemble a single general defense framework. In other cases, states assemble multiple DCAs in piecemeal fashion. What explains the choice between these two options? Institutional design concerns permeate DCAs, including questions of treaty duration, ease of termination, prospects for renewal, and, of course, scope. Are these features a consequence of regime type, development, pre-existing legal commitments, or other influences? Might these design features themselves be potentially endogenous to the network? I have argued that network ties convey information on design preferences, which suggests that particular institutional features may diffuse throughout the network and, via this diffusion process, emerge as equilibrium design choices for states. That is, not only do pre-existing DCA ties encourage the formation of new DCAs; they might also encourage the formation of specific types of DCAs.
Finally, the influence of DCAs is almost certainly not restricted to defense-related issues. DCAs are often signed alongside an array of other agreements, including extradition treaties, double taxation treaties, counterterrorism agreements, and investment treaties. There is thus a possibility of issue linkage between DCAs and other agreement types.Footnote 121 Countries may hold out DCAs as a security-oriented reward for cooperation in economic or other areas. Or countries may reward DCA ratification with subsequent investment or other financial deals. The possibilities are numerous and largely unexplored.
Supplementary Material
Supplementary material for this article is available at <https://dataverse.harvard.edu/dataverse/bkinne>.