Book contents
- Frontmatter
- Contents
- Preface
- Part I Secure Multiparty Computation
- 1 Introduction
- 2 Preliminaries
- 3 MPC Protocols with Passive Security
- 4 Models
- 5 Information-Theoretic Robust MPC Protocols
- 6 MPC from General Linear Secret-Sharing Schemes
- 7 Cryptographic MPC Protocols
- 8 Some Techniques for Efficiency Improvements
- 9 Applications of MPC
- Part II Secret Sharing
- List of Algorithms
- List of Exercises
- References
- Index
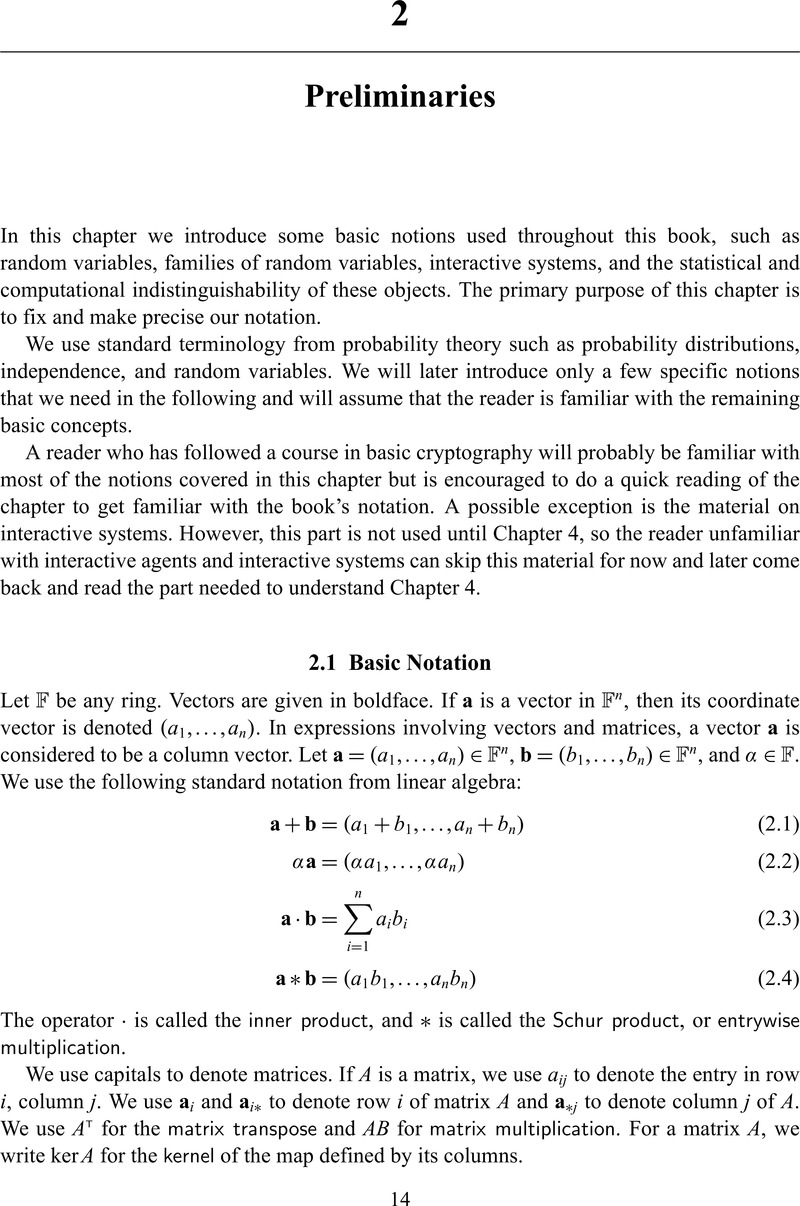
2 - Preliminaries
from Part I - Secure Multiparty Computation
Published online by Cambridge University Press: 05 August 2015
- Frontmatter
- Contents
- Preface
- Part I Secure Multiparty Computation
- 1 Introduction
- 2 Preliminaries
- 3 MPC Protocols with Passive Security
- 4 Models
- 5 Information-Theoretic Robust MPC Protocols
- 6 MPC from General Linear Secret-Sharing Schemes
- 7 Cryptographic MPC Protocols
- 8 Some Techniques for Efficiency Improvements
- 9 Applications of MPC
- Part II Secret Sharing
- List of Algorithms
- List of Exercises
- References
- Index
Summary
- Type
- Chapter
- Information
- Secure Multiparty Computation and Secret Sharing , pp. 14 - 31Publisher: Cambridge University PressPrint publication year: 2015

